Schedule Your Demo
Unleash the power of team building and interactive learning with Living Security’s immersive and virtual training with CyberEscape Online.

Serving customers across industries
Proactive Cybersecurity: “Left of Boom”
LivingSecurity is transforming how CISOs can exercise continuous diligence in reducing human risk by proactively protecting their data and infrastructure to the “left of boom”, i.e., before a costly and dangerous incident.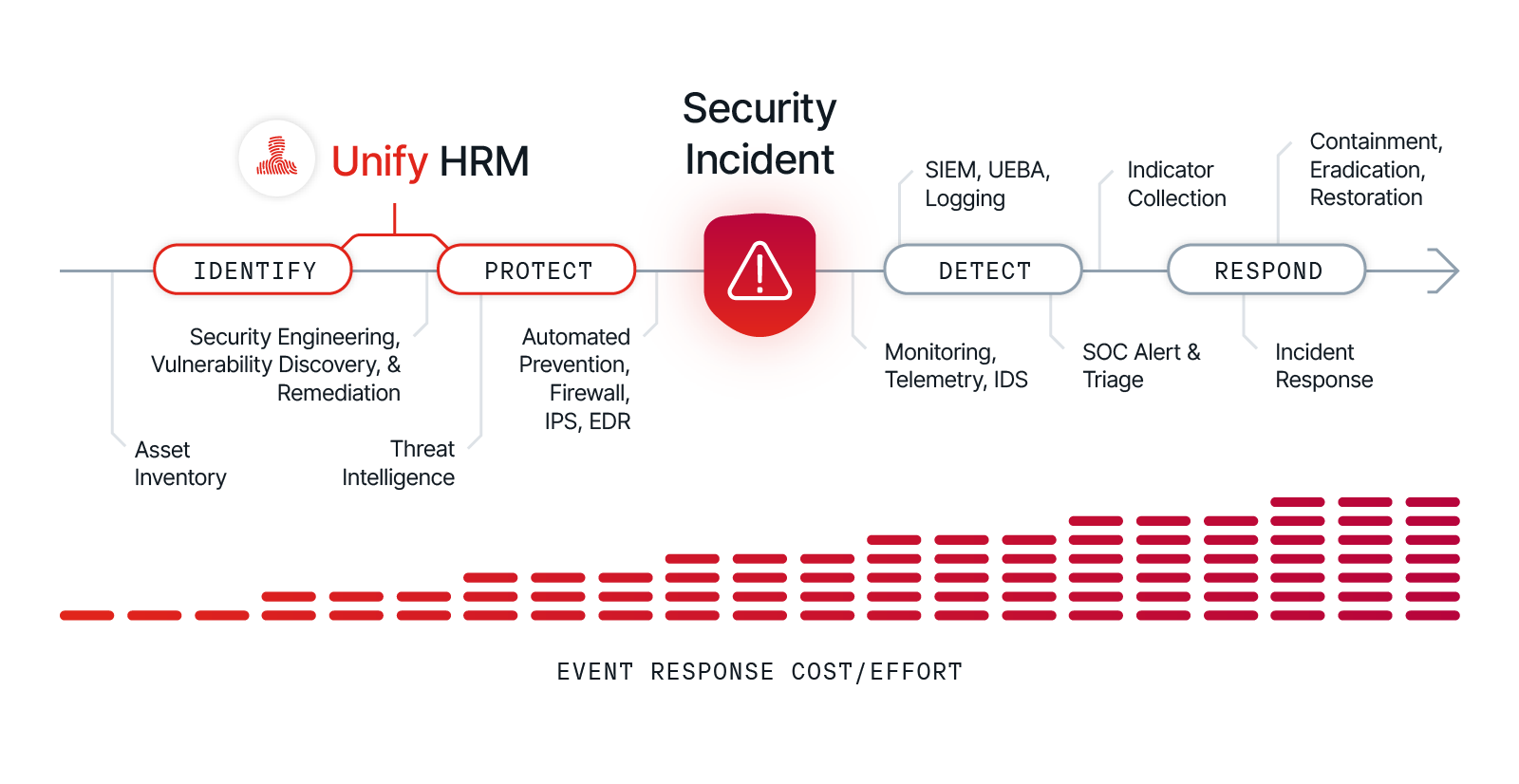
Human Defense
starts with Living Security
 Identify
Identify
.png) Protect
Protect
 Report
Report


Since working with Living Security, Cybersecurity Awareness Month is way, way easier than it used to be. Our team used to lose sleep every October. We see higher-than-expected engagement with the speakers and training provided in the Living Security Program.
Alaina DeGregory, Enterprise Risk & Governance
Human Risk Management
The Living Security Difference
Full Cycle HRM Platform
Living Security transforms the vast array of human risks spanning data loss, malware, phishing, and identity threats into predictive insights that identify the full array of risky behaviors across your workforce and initiate preventive actions that protect employees in need through a single platform, not universal one-size-fits-all training.
The Unify HRM platform offers multiple options that enable you to rapidly start your human risk management journey with Unify Go and progressively grow in minimizing the full scope of workforce vulnerabilities with Unify Enterprise
Most Engaging Content, Hands Down
Train smarter, not harder with Living Security. Designed to engage users with immersive live-action video and a personalized approach, users can choose from a variety of entertaining and effective modules that enhance engagement and comprehension.
Tailoring learning based on roles, industries, and specific risk areas helps drive behavioral change and tackle modern threats. Setting up training campaigns is easy with contextual reminders and ready-to-use templates in multiple languages to ensure you can meet the needs of our global workforce.
Phishing Simulations
Whether it’s phishing, smishing, or vishing, Living Security helps you empower employees to become cybersecurity heroes through realistic training simulations, across multiple channels, to learn how to identify and shut down these types of attacks.
Living Security integrates seamlessly with your existing security tools, offering a comprehensive, ready-to-use or custom scenarios in multiple languages to build a unified defense against the ever-evolving threats.

Compare Living Security
Many organizations rely on Security Awareness Training (SAT) and phishing simulations – valuable tools, but limited in scope. Here's where Living Security steps in.
Living Security's Unify platform moves beyond traditional training, offering a data-driven approach to reduce human-led risk and build a culture of cybersecurity awareness. Let's explore how Unify compares to other solutions on the market.




Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
100% objective, data driven insights in to Human Risk
100% objective, data driven insights in to Human Risk
100% objective, data driven insights in to Human Risk
100% objective, data driven insights in to Human Risk
100% objective, data driven insights in to Human Risk
100% objective, data driven insights in to Human Risk
100% objective, data driven insights in to Human Risk
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Risk Based Interventions with Training Nudges and Policy Change etc.
Risk Based Interventions with Training Nudges and Policy Change etc.
Risk Based Interventions with Training Nudges and Policy Change etc.
Risk Based Interventions with Training Nudges and Policy Change etc.
Risk Based Interventions with Training Nudges and Policy Change etc.
Risk Based Interventions with Training Nudges and Policy Change etc.
Risk Based Interventions with Training Nudges and Policy Change etc.
Slack and Microsoft Teams Integration for Communications
Slack and Microsoft Teams Integration for Communications
Slack and Microsoft Teams Integration for Communications
Slack and Microsoft Teams Integration for Communications
Slack and Microsoft Teams Integration for Communications
Slack and Microsoft Teams Integration for Communications
Slack and Microsoft Teams Integration for Communications
Manager and Employee Scorecards
Manager and Employee Scorecards
Manager and Employee Scorecards
Manager and Employee Scorecards
Manager and Employee Scorecards
Manager and Employee Scorecards
Manager and Employee Scorecards
Comprehensive and Engaging Video Content Library (Compliance + )
Comprehensive and Engaging Video Content Library (Compliance + )
Comprehensive and Engaging Video Content Library (Compliance + )
Comprehensive and Engaging Video Content Library (Compliance + )
Comprehensive and Engaging Video Content Library (Compliance + )
Comprehensive and Engaging Video Content Library (Compliance + )
Comprehensive and Engaging Video Content Library (Compliance + )
Monthly Campaign in a Box (New monthly content + Marketing material)
Monthly Campaign in a Box (New monthly content + Marketing material)
Monthly Campaign in a Box (New monthly content + Marketing material)
Monthly Campaign in a Box (New monthly content + Marketing material)
Monthly Campaign in a Box (New monthly content + Marketing material)
Monthly Campaign in a Box (New monthly content + Marketing material)
Monthly Campaign in a Box (New monthly content + Marketing material)
Cybersecurity Escape Rooms
Cybersecurity Escape Rooms
Cybersecurity Escape Rooms
Cybersecurity Escape Rooms
Cybersecurity Escape Rooms
Cybersecurity Escape Rooms
Cybersecurity Escape Rooms
Phishing Simulations
Phishing Simulations
Phishing Simulations
Phishing Simulations
Phishing Simulations
Phishing Simulations
Phishing Simulations
Phishing Detection and Response (Orchestration)
Phishing Detection and Response (Orchestration)
Phishing Detection and Response (Orchestration)
Phishing Detection and Response (Orchestration)
Phishing Detection and Response (Orchestration)
Phishing Detection and Response (Orchestration)
Phishing Detection and Response (Orchestration)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
100% objective, data driven insights in to Human Risk
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Risk Based Interventions with Training Nudges and Policy Change etc.
Slack and Microsoft Teams Integration for Communications
Manager and Employee Scorecards
Comprehensive and Engaging Video Content Library (Compliance + )
Monthly Campaign in a Box (New monthly content + Marketing material)
Cybersecurity Escape Rooms
Phishing Simulations
Phishing Detection and Response (Orchestration)
Integrations in to Enterprise Security Tech Stack (Ecosystem Agnostic)
100% objective, data driven insights in to Human Risk
Human Risk Visibility Beyond Email Phishing (Identity, Malware, Data Loss etc.)
Risk Based Interventions with Training Nudges and Policy Change etc.
Slack and Microsoft Teams Integration for Communications
Manager and Employee Scorecards
Comprehensive and Engaging Video Content Library (Compliance + )
Monthly Campaign in a Box (New monthly content + Marketing material)
Cybersecurity Escape Rooms
Phishing Simulations
Phishing Detection and Response (Orchestration)
